This article attempts to stimulate your choice over the relevant field and to offer you more innovative cyber security dissertation ideas. Cybersecurity involves the practices of securing a group of equipment and methodology to devices, and information prevents mutilation to the system or networks by the unverified use and re-establishing the electronic data and communication systems.
In general, the primary function of the information in a system is to confirm the device’s privacy and security. It also involves the security and re-establishment of whatever the medium of the network like wired or wireless, satellite. The system policy control solution can react to identify the network traffic and user activity. Those things are grounded on real-life threat intelligence information to secure user’s data from phishing, malware attack, intruding the botnet command and server leverage.
What is Cyber security?
The cybersecurity objectives secure computers, networks, and mobile devices from malicious access and users. It also controls the use of stolen data in cyberspace. Adversaries use the hacked network or device to spy on the individual or organization’s activity and to control them by all means. The common attacks performed by the cybercriminal to damage the network are as follows,
- Drive-by downloads
- Malvertising
- Man in the Middle
- Distributed Denial of Service
- Phishing
- Password attacks
- Malware

Cyber Security Research Guidelines
- Cybersecurity: Prevention, identification and controlling procedures
- Incorporeal methods in Cybersecurity
- Cybersecurity theories
- Technology in cybersecurity
- Cybersecurity strategy and management
- Events of cybersecurity
- Applications of Cybersecurity
The above fields are involved in Cybersecurity. So, providing cyber security dissertation ideas induces the vast chances of the scholars and students to get more knowledge about the relevant field. We provide you more about the functions of Cybersecurity, its mechanisms, and Cybersecurity in further platforms. Précising the exposed issues in the cyber security dissertation, and we highlight the research challenges in predicting Cybersecurity as follows,
What are the research challenges of cyber security?
- What are the metrics and ways to assess or forecast cyber security model?
- What should be forecast? Whether viewing the cybersecurity scenario globally or the new attacker in cyber security domain, or the attacker’s next step?
- What are the uses of cyber security prediction and its effectiveness?
Our research team identifies the above questions as research gaps in Cybersecurity. If you select the project, you must answer the above questions that remained unanswered in the research domain of Cybersecurity, Or else, we provide you the latest ideas on the associated topic.
Why to use Cybersecurity Models?
- Unverified users will be prevented by cyber security
- Induces the post-attack recovering time
- Cybersecurity protects networks and data
- Provides end-user security
- Cybersecurity gives data protection from social engineering, malware and phishing
The usage of the cybersecurity model mitigates the effects of pre-attack and post-attack scenarios, and it also provides the necessary time for data recovery. The functioning process of the cybersecurity model varies according to the threat effect. The further operations of the Cybersecurity research model are as follows,
Working of Cybersecurity model
- Real-time observation collecting data based on
- Cyber features
- Logs on file integration
- Logs on system incidents
- Logs of protection
- Physical features
- Messages on system health
- Critical alerts
- Cyber features
- Detecting anomalies
- Homogeneous correlation
- Analysis similarity to file integrity logs
- Analysis similarity to system incident logs
- Analysis similarity to the logs of security incidents
- Heterogeneous correlation
- Analysis similarity to various types of control center logs
- Analysis similarity to control center and substations logs
- Homogeneous correlation
- Analyzing impacts
- Causes of cyber attacks
- Effects of cyber attacks
- Mitigation / prevention methods
- Suspending the untrusted users
- Role changing on licensed users
Cybersecurity models are skilled to perform the above-mentioned actions for securing, detection, recognition, modification, and recovery. There are many sub-tasks under each function of cybersecurity models, which may vary according to their usage. Let’s have a look at the emerging methodologies in Cybersecurity.
Emerging technologies in Cybersecurity
- Evaluating confidential threats
- Assessing penetration
- IPS and IDS
- Blockchain
- Attacks against phishing
- Predicting events and intrusions
The above-mentioned technologies are also the processing steps that are using in the on-growing cybersecurity technology. They perform the actions to block unauthorized access, phishing attack, intrusion detection testing, etc. Cybersecurity tools can execute those technologies. This also involves some theoretical mechanisms too. For your clear reference, our technical team has particularized the theories below,
What are some Cybersecurity mechanisms?
- Fuzzy Decision Theory
- Evolutionary Theory
- Evidence Theory
- Dempster- Shafer Theory
- Danger Theory
- Complex Networks Theory
- Decision Making Theory
- Immune Theory
- Grounded Theory
- Grey Theory
- Graph Theory
- Game Theory
- Theory Of Contextual Integrity
- Stakeholder Theory
- Sociomaterial Theory
- Integrated System Theory
- Instance- Based Learning Theory
- Rational Decision-Making Theory
These theories can be executed in Cybersecurity on the basis of the attacker’s behavior. So, the functions of the theories also may vary according to the changes in the adversarial activities. Here we provide you our latest cyber security dissertation ideas.
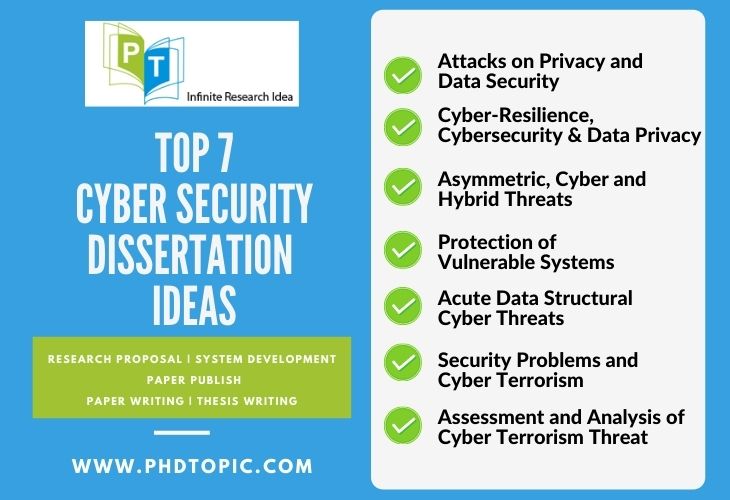
Latest Cyber Security Dissertation Ideas
- Attacks on Privacy and Data Security
- Cyber-Resilience, Cybersecurity and Data Privacy
- Asymmetric, Cyber and Hybrid Threats
- Protection of Vulnerable Systems
- Acute Data Structural Cyber Threats
- Assessment and Analysis of Cyber Terrorism Threat
- Security Problems and Cyber Terrorism
The ideas discussed above are our trending Cyber security dissertation ideas. Our expert research team considers the ideas as an exposed range of dissertation topics that remain unexplored. We have world-class certified engineers to help you with the dissertations ranging from the initial to the final stage. We have 200+ technical employees, including project developers, writers, engineers, research, and technical team. Here they provide you the best tools for data collection as follows,
Cybersecurity Tools for Data Collection
- EtherApe realistically displays the network behavior in detail
- Dsniff is a tool to analyze both network and password
- TCPDUMP used for transmitted packet analysis
- MSN Sniffer 2 is considered as the first tool to sniff chats
- Ettercap suits in the attack simulation of man in the middle
The attackers use the above-mentioned data collecting tool to perform various types of attacks. Tools may vary according to the attack. Here we offer you the extending levels of the performance of Cybersecurity. The performance relies on the major functions of the cybersecurity tool as follows.
Cybersecurity Performance Metrics
- Metrics to Resilience
- Analyzes the “in between time of recovery, response and intrusion”
- Analyzes the functional level at the pre-attack and post-attack scenarios
- Metrics to security
- Analyzes the security aims attained by the system
- Analyzes how its best in functioning the key security
- Metrics to risk
- Analyzes hacker’s attack and similar scenarios
- Analyzes the risk impact
The above metrics denote the fundamental function of the cybersecurity model, other than the mentioned metrics; our developer’s team suggests some evaluated metrics are as follows. Its primary function is to conduct deep analysis on time taken after each event of an attack and recovery; some organizations also use it to measure the team’s potential.
Cybersecurity Evaluated Metrics
- Mean Time To Recovery (MTTR) analyses the time taken to recover from system failure by an organization
- Mean Time To Contain (MTTC) analyses the vector attacking time
- Mean Time To Acknowledge (MTTA) analyses the time take to resolve the issue once the alert is received.
- Mean Time To Resolve (MTTR) analyses the time taken by the cybersecurity team to resolve threats
- Mean Time To Detect (MTTD) analyses the time of existence by an attack. It also uses to analyze the cybersecurity team
- Mean Time Between Failures (MTBF) analyses the time taken in between the system failure and decision making
- No of Intrusion Trials analyses the no of intrusion
The above-assessed metrics particularized by our research team can be used only to analyze the time before or after the attack and in between times consumed by the cybersecurity teams. Getting knowledge of these metrics will be helpful for your cyber security dissertation ideas. Along with your existing knowledge, we would provide you the ways of our support and guidance in cyber security dissertations when you work on your thesis with us.
How do we support for dissertation writing?
- Initiating research topic with essential background information
- Develops the concentration on the research scope
- Viewing the relevance of the research to an existing broader issue and describes the level of existing research on the topic
- Clearly describing aims and research questions
- Providing dissertation structure overview
- Progresses and reinforces existing knowledge with our new data
- Chooses a new approach to the topic either of theoretical or technical
- Suggest solutions to unsolved issues
- Progresses a theoretical and practical investigation
- Conclude the dissertation by covering all ideas
We offer our extending guidance in familiarizing you with the other researching areas of Cybersecurity based on your interest. We assure you of our years of reputation to render your expected research outcomes. Working with us will afford you on-time delivery of your project begins with cyber security dissertation ideas with confidential service. Our research team also suggests your thesis’s practical implementations without letting you worry about the research scope. So we insist you grab the opportunity to work with us!!
