RPL PROTOCOL TUTORIAL CODE
RPL Protocol Tutorial Code is created for final year students and research scholars to reach their destination. RPL (Routing Protocol for Low-Power and Lossy Networks) is a standardized routing protocol that is mainly designed for 6LoWPAN networks (IPv6 over Low-powered Wireless Personal Area Networks. Our company has ISO 9001.2000 certification also with continuous improvement and 100% customer satisfaction.
We also have 150+ experts who study, develop, execute, and run RPL protocol projects for students’ academic careers. And also, We are experienced in providing fully-fledged final year projects. Contact us!!! We are a pleasure at being worked for you…
Here we provided some valuable information to start your RPL protocol projects,
There are four research challenges are focused on RPL:
- QoS aware Routing (Constraints also based Routing)
- Security (Preinstalled, Unsecured and also Authenticated)
- Fault Tolerance (DODAG Repair, Loop Avoidance and also Detection)
- Load Balancing (Network Traffic Balancing)
 FAIRLY WELL-KNOWN RPL ATTACKS
FAIRLY WELL-KNOWN RPL ATTACKS
Resource-based Attacks
- Flooding attack
- Rooting table overload also in attack
- Increased rank attack
- DAG inconsistency also in attack
- Version number modification also in attack
Traffic Anomalies-based Attacks
- Sniffing attack
- Denial of service also in attack
- Distributed Denial of Service (DDoS) attack
- Traffic analysis attack
- Identity attack
- Decreased rank also in attack
Topology Disruptions based Attacks
- Routing table falsification attack
- Sinkhole attack
- Blackhole attack
- Route information reply also in attack
- Wormhole attack
- DAO inconsistency attack
Major Security Research Challenges
- Lack of authentication
- Data privacy (Encryption based and also Anonymization based)
- Data-collection (Blocking and also lightweight approaches)
- Insecure cloud or mobile interface integration
- Data sharing and management (Semantic web, P3P (Platform also for Privacy Preferences))
Future Research Directions for RPL
- Lightweight distributed computing techniques
- Two-factor/Multi-factor authentication
- Secret session establishment
- QR-code also based authentication
- Real-Time events monitoring also using cyber sensor
- RFID-based authentication
- Bio-metric based authentication
-Eye texture recognition
-Fingerprints identification
-Voice recognition
-Face recognition
-Iris recognition
-Hand patterns recognition
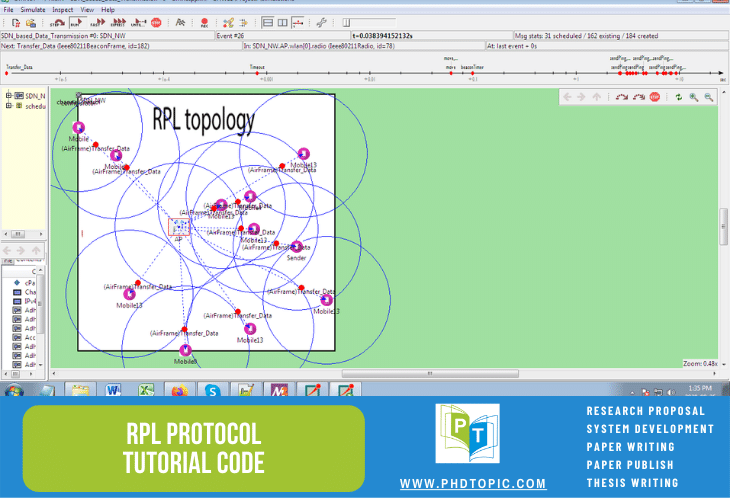
Tutorial Code in RPL Protocol
RPL Protocol Tutorial Code is a well-established emerging platform started for budding students and also PhD scholars. Cooja Simulator is also a special network simulator supporting RPL over the Contiki OS. In Cooja simulator can run at three levels at a time: network level, operating system level, and also machine code instruction level, but the other network simulators (AURORA, NS2, and also TOSSIM) can run anyone level at a time.
RPL Protocol under Contiki OS Cooja Simulation
- It also uses different motes firmwire within the rpl-collect directory
- Source code motes directory – Contiki/examples/ipv6/rpl-collect
- Source code malicious – ContikiX/examples/ipv6/rpl-collect
- It also supports Wireshark Network Analyser (to capture network traffic)
- Roles of Tmote Sky mote roles
-Sink mote
-Leaf mote
-Malicious mode
Parameters for RPL QoS Measures
- Latency
- Throughput
- PDR (Packet Delivery Ratio)
- Power consumption
- Convergence time
- ETX (Expected Transmission Count)
- Control traffic overload
Our Newfangled Research Topics for RPL
- A Novel Architecture also for RPL Protocol based Networks in a Hybrid Mode of Operation
- An Extended Mechanism also for Mobility Support for Downward Traffic Monitoring and Analysis in RPL Networks
- Constructing Attack Graph also for Rank Property Assessment in RPL-6LOWPAN for Internet of Things
- Analysis of RPL Objective Functions Performance also for Various Sending Intervals under Contiki Cooja Simulation
- Development of Mobile Internet of Things Applications also using Game Theoretic Optimization in RPL networks
- Detection and Prevention of DAO Inconsistency Attack also for RPL networks
- Evaluation of Effects and also Challenges in Wormhole Attack against RPL routing protocol
- A New Technique also for Forwarding Misbehaviors Mitigation for RPL-based Low power and Lossy networks
- Cross-layer and Power Control Design also for Low Power and Lossy Networks based on Objective Functions on RPL
- Mitigating a DoS Attack (Hatchetman attack) against RPL Networks also using Cooja Simulator
